Exploring bleeding edge experiments, oddities, new and bizarre dicoveries, and fact-checking conspiracy theories since 2008. No question is out of bounds and no topic is too strange for a deep dive.
# tech
We’re told that digital security is a cat and mouse game between computer geniuses, but the reality is a lot less impressive and sadder than we’re led to believe.
# tech
While most apps you use today collect a lot of data, TikTok goes far beyond normal logging and location services, and straight into the realm of spyware.
# tech
With the EARN IT bill, politicians are unwittingly and stubbornly putting us at greater risk from criminals and terrorists while insisting they’re just trying to protect us.
# podcast
If we compromise encryption standards used to secure almost everything we do electronically, we'll catch more criminals. But we'll also create millions more by giving them easy targets.
# tech
Resistance to Huawei's technology being implemented across the world for new 5G networks isn't xenophobia or tech feudalism. It's a sober stance based on China's behavior.
# tech
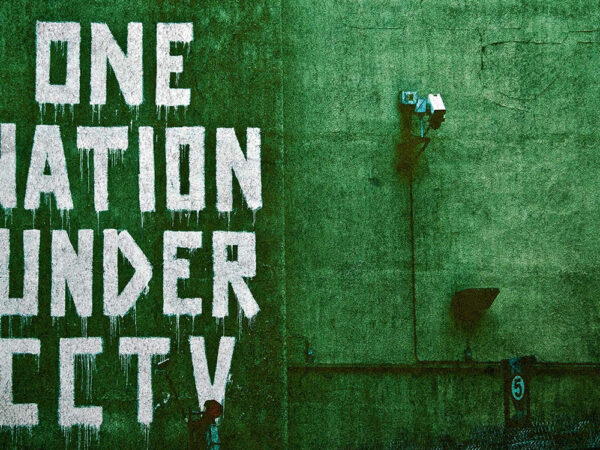
Law enforcement agencies can’t wait to deploy facial recognition AI in daily policing, and pressuring lawmakers to get out of their way. But their zeal for face-seeking AI can easily backfire.
# tech
In the next ten years or so, your internet experience will be the same as today. But that internet may be built on complex quantum interactions instead of bits and bytes flying between routers and servers.
# tech
Gadgets connected to the internet and controlled by apps are everywhere, even in things that don’t need to be linked global communication networks. Unfortunately, they’re not working out well for us...
# tech
Threatened by the open, permissive architecture of the internet, Russia is doing a dry run at building its own. If it succeeds, the effects on the global economy and geopolitics would be far-reaching and unsettling.
# tech
Australian lawmakers stunned the country’s techies by passing a law requiring them to help law enforcement snoop on encrypted data on request, and putting e-commerce and basic digital security at risk.