cybersecurity done horribly wrong, revisited
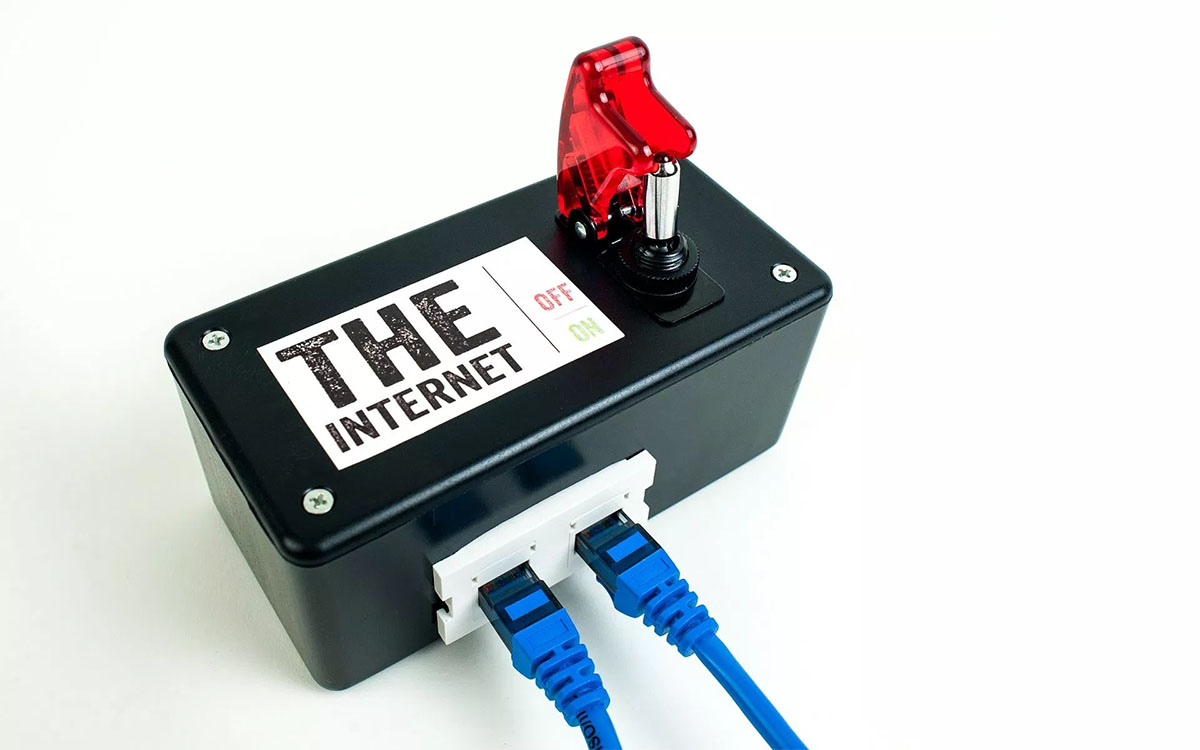
Humans have a long history of bad ideas including our attempts to treat the plague with leaches, blaming the mentally ill for being possessed by demons, the Inquisitions, and a whole lot of other things we could spend weeks listing. Among all those bad ideas, we should also count the newly resurrected internet kill switch bill, which was concocted last year by Joe Lieberman and managed to show absolutely zero awareness of what the internet is or how it actually works. It seemed as if Lieberman read something about Chinese hackers trying to get into American servers and acquire some militarily useful intelligence, decided that damn it, he’s going to do something about it, and without consulting anyone with a passing clue of networking, drafted the fanciful notion of some big, red button that the President can press to shut off the internet and stop the hordes of foreign evildoers trying to wreck the nation’s infrastructure from coffee shops in Beijing or Moscow. And just to add insult to injury, the bill actually had sponsors who also seemed to know nothing about the internet and why it’s not just a really long series of winding tubes you can just shut off with a strategic valve on a whim.
You would think that in the wake of Mubarak’s crackdown on internet access and it’s failure to stop Egyptians from getting on Facebook and Twitter, the lawmakers seriously proposing the kill switch idea would consider the fact that it’s impossible to shut off every modem and smartphone in the country and that perhaps, it could be a good use of their time to learn a little something about how internet connectivity works. You can’t place a kill switch on it because by its nature, the internet is decentralized and since we use it so much, we just keep forgetting that it was invented as a military communication tool designed to keep commanders connected in the event of a massive nuclear bombardment which destroys existing communication networks. Try to block signals coming in or out of your country’s networks, and you’ll find that there’s always some work-around and the data packets can either be spoofed to go around your firewalls, or simply take another route to get where they were sent to go. That’s what makes the internet great. But instead of learning the appropriate lesson, the proponents of the kill switch decided to prove that they based their idea on too many action movies…
But proponents of the American bill countered that they would never want a shutdown on Egyptian lines. Laws that govern radio and television broadcasts already give the American authorities the right to shut bits of the internet, they argue. The new bill merely clarifies and limits such powers. These would be needed, for example, if hackers took control of nuclear facilities, or were about to open the Hoover dam.
Right, because nuclear reactors, dams, and power grids could be magically accessed online and just like in the movies, pressing keys really fast on your keyboard and hitting a random button with an excited yelp would shut off all power to North America or give you a dashboard from which you could steer a nuclear reactor into meltdown the size of Chernobyl. Now I know that Live Free or Die Hard might have been a fascinating movie, but it’s not exactly a good, reasonable, or even remotely accurate instruction manual on cyber warfare. If you’d like to know what Hollywood thinks computers could do, you should take a look at the Tron sequel’s creative re-interpretation of basic computer science. In the real world, critical infrastructure nodes would more likely be felled by something like Stuxnet, a custom-designed saboteur program intended to subtly disrupt ongoing processes and nudge very complicated hardware to do something it’s not supposed to do. Simply hacking in and hijacking a SCADA machine or an industrial computer, which is very seldom connected to anything other than the device it’s intended to control, is the realm of fiction. All an internet kill switch would do is disrupt the day’s ongoing business transactions while mildly inconveniencing a hacker who’ll now need another proxy or a few spoofed packets to finish whatever he or she was doing.





